WHY HARD DRIVE SHREDDING SHOULD BE LEFT TO THE EXPERTS
Businesses often use hard drives to store confidential customer, company or financial information that would be detrimental if data thieves were to access it.
When they need to dispose of electronics that have reached the end of their usefulness, it’s crucial to properly wipe or destroy the hard drive data. Otherwise, they risk legal liability, fines, and reputation damage.
Unfortunately, simply erasing data from a hard drive does not ensure complete protection. Often, trace to large amounts of data can linger long after the necessary steps to erase the information. That’s why certified electronics recyclers commonly use a technique called hard drive shredding to guarantee all traces of data are safely and securely destroyed.
Read MoreLOCK AND KEY: HOW THE NIST 800-88 DATA DESTRUCTION STANDARD SAFEGUARDS YOUR DATA
Recent high-profile data breach cases have shown that data security and secure data destruction are often overlooked—but critical—aspects of IT asset disposition (ITAD). But what exactly is involved in secure data destruction, what standards are a certified electronics recycler held to, and how can you ensure that your data is absolutely secure in the IT asset disposition process?
Here, we provide a look at the rigorous requirements of the NIST 800-88 data destruction standard and why it is critical for your electronics recycler to possess this essential certification.
Read MoreTHE ANSWERS TO YOUR QUESTIONS ABOUT HARD DRIVE SHREDDING
When should you select hard drive shredding? We answer that and more in this post.
With millions of electronic devices reaching the end of life every year, businesses inevitably question what to do next. High-profile data breaches, fines for inappropriate handling of protected data, and environmental concerns have brought electronic recycling into the spotlight.
In return, businesses have become increasingly aware of the importance of prioritizing the disposition of their obsolete IT assets, including the need for data destruction. Many of the questions that we receive concern hard drive shredding:
- How does hard drive shedding work?
- When should it be performed?
- How do I know the job was done right?
- Are there other methods?
Let’s get to the answers:
How does hard drive shredding work?
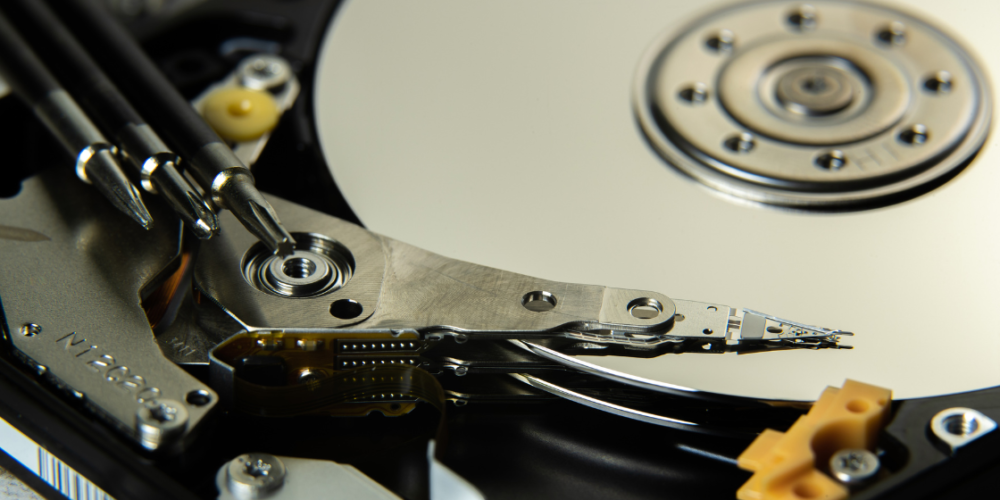
DIY is not an option
First of all, we need to make clear what hard drive shredding is not. Taking a hammer to a hard drive or piercing it with a drill does not constitute adequate destruction. This still needs to be said as we do come across businesses which — well-intentioned as their effort may be — think the do-it-yourself methods can take the place of professional shredding. Similarly, simply erasing hard drives prior to disposal does not stop third parties from retrieving the data.
Certified partner, right equipment
In fact, only mechanical destruction performed by a certified partner with the right shredding equipment can guarantee absolute security. At Global Electronic Recycling, we use the Untha Industrial Shredder. This top-of-the-line shredder shreds hard drives to NIST 800-88 and the DIN 66399-2 standards (destruction systems for files and data carriers).
As a result of the high flexibility of the four-shaft shredder, we can also shred other optical storage media such as SD cards, Blu-Rays, and USB sticks. Its compact construction further enables us to bring the shredder to you to perform the job on-site.
Shredding the drives
In short, we remove hard drives from the device (computer, laptop, server) and place them in the shredder. This subsequently renders them completely destroyed and the data completely unrecoverable. We then recycle the debris.
When should it be performed?
The short answer:
- Hard drive shredding is the ideal option for highly secure or sensitive data with compliance related to finance, national security, and HIPAA.
- It’s also a good fit for those who would like to witness the destruction being performed in real time. Witnessed destruction provides extra reassurance that everything is done by the book. In the case of GER, our military-trained and classified-asset-destruction team is on-site to protect your brand name and sensitive data every step of the way. Additionally, our secure chain of custody includes a fully auditable paper trail, end-to-end visibility, and a Certificate of Destruction.
If, on the other hand, you’re under no such regulatory constraints, you are better off pursuing other methods that let you recoup value (see more on this below).
Data breaches
If your business ignores regulations to pursue hard drive destruction, you do more than risk steep fines for noncompliance. A study by the National Association of Information Destruction (it has since merged with another trade group to become the International Secure Information Governance & Management Association, i-SIGMA) showed more than 40% of used electronic devices sold in secondary markets contained personally identifiable information and protected health information.
Even more concerning, the process used to retrieve the data required no advanced forensic training. The researchers easily uncovered usernames, passwords, credit card data, tax details, and contact information on used hard drives, mobile phones, and tablets.
Only option
However, a professional, R2-certified electronic recycler that wipes to NIST 800-88 will eliminate any risk of the above and achieve absolute data destruction. But, again, for your most highly sensitive data, some state and federal regulations will give you no choice but to select hard drive shredding.
How do I know the job was done right?
Don’t leave without a Certificate of Destruction (COD). A tamper-proof certificate is your final verification of absolute data destruction in compliance with NIST 800-88.
At GER, we authenticate data destruction through the issuance of data destruction reports and certificates, including a Certificate of Destruction. The certificate includes information on the shredding process, serial numbers of shredded drives, data and time of the job, and the name of the team member who performed the service.
Are there other methods?
When it comes to data destruction — yes, there are other methods. But there’s nuance to this answer. As we wrote in the previous paragraphs, state and federal regulations may limit your options.
Let’s take a look at two more data destruction methods:
Degaussing
In some cases, regulations may call for degaussing. Degaussing is a form of physical destruction. And just like hard drive shredding, it leaves the drive unfit for resale and should be a last resort.
Degaussing renders data unrecoverable by using a highly powerful magnetic field to permanently remove magnetic properties from the iron oxide or chromium dioxide coatings. Once the method has erased the recorded data pattern, we dismantle the hard drive and recycle its components. Degaussing is, for some companies, the only way to satisfy a federal requirement related to the destruction of clearance-level information (“Classified” or “Top Secret”).
Data Erasure/Wiping
For companies that seek to recoup value in secondary markets, this is the method of choice. Since it involves no physical destruction, the sanitized equipment safely enters resale platforms in good condition. In addition to increasing resale value, data erasure/wiping also generates no e waste. With increased focus on sustainability and reducing carbon footprints, you can leverage this method to raise your green profile.
Unless regulations demand that you choose another method, we often recommend data wiping for this reason.
Please reach out with any questions
Do you have more questions about hard drive shredding or any other services related to electronic recycling? We’re here to help. Contact us today.
Read more
YOUR QUICK GUIDE TO THE NIST 800-88 DATA DESTRUCTION STANDARD
NIST 800 DATA DESTRUCTION: THE METHODS THAT COMPLY
WHEN SHOULD YOU PURSUE HARD DRIVE SHREDDING SERVICES?
SEEKING ABSOLUTE DATA DESTRUCTION? LOOK FOR CERTIFIED ERASURE.
For your most sensitive data, seek verification of absolute data destruction and beware of methods that don’t fulfill data sanitization requirements.
How can I know my business data has been completely erased and is irrecoverable even with the most sophisticated methods? We get questions along those lines quite often and our answer goes something like this: absolute data destruction includes more than the secure erasure of data. The solution must also verify its successful completion and produce an auditable, tamper-proof certificate of destruction to prove compliance with global regulations.
WITNESSED DESTRUCTION OF IT ASSETS: HOW IT IS DONE
For added peace of mind, witnessed destruction lets you monitor the permanent destruction of your most sensitive assets and data
A common query that we receive is about witnessed destruction. How do I know sensitive data has been destroyed? Can I observe the process myself? How does it work? Do I receive some type of verification? To answer those questions, we wrote this blog post.
Read More