5 COUNTERFEIT SCHEMES COMPANIES NEED TO WATCH OUT FOR
A number of products are frequent targets of counterfeit schemes. Don’t let them take advantage of your business.
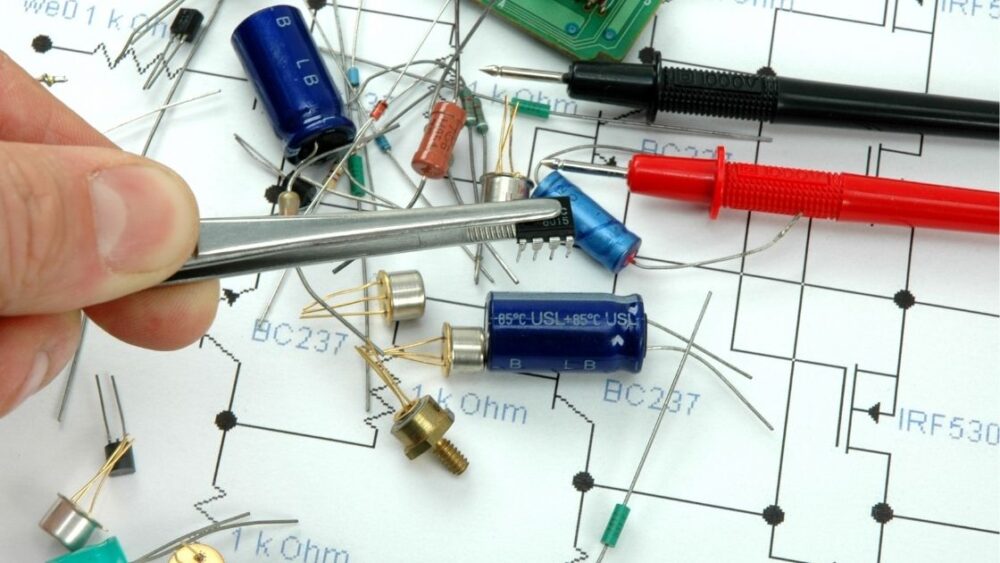
When you work in electronics authenticity testing, you realize there’s a lot of ingenuity out there, only all too often it’s used for insidious purposes. The black market for counterfeit electronics is big business. Trade-in counterfeit and counterfeit goods now stand at 3.3% of global trade, according to OECD. And the electronics industry is the fourth hardest hit by counterfeit schemes, just after footwear, clothing, and leather goods.
AUTHENTICITY TESTING IS CRUCIAL TO COUNTERFEIT DETECTION. HOW IT’S DONE.
Increasingly sophisticated schemes require authenticity testing to keep fake parts out and protect your business reputation
Counterfeit parts are now so common the question is hardly “if” but “when” they will cross paths with your electronic products.
Ironically, one of our team members — an expert in authenticity testing — recently ran into a common scheme on a large online reseller platform. In this case, the buyer accused him of sending a counterfeit in an attempt to start an exchange process. During the process, the buyer himself tried to send back a counterfeit product in return for one with authentic parts.
Read MoreGER AIMS TO BECOME A CERTIFIED B CORP. WHY IT MATTERS.
The B Corporation Certification sets the gold standard for good business. Now, GER seeks to join the race to the top.
At Global Electronic Recycling, we call ourselves the “GER team” for a reason. The way we treat each other is, after all, a telling indication of the way we treat our customers. When our team members thrive, so will your business. Now, we seek to make official our effort to be a force for good.
Earlier this year, we decided to pursue a B-Corporation Certification. Certified B Corps are businesses that meet the highest standards of verified social and environmental performance, public transparency, and legal accountability to balance profit and purpose.
With a B-Corporation Certification, GER will join the likes of Patagonia, Stonyfield, Eileen Fisher, and close to 4,000 other companies across 150 industries that have committed to using profits and growth to build a more sustainable and inclusive economy.
The requirements are strict. Only 1 in 3 companies that submit for certification succeed. That’s because certifying as a B Corporation goes beyond product- or service-level certification. B Corp Certification is indeed the only certification that measures a company’s entire social and environmental performance.
Taking the impact assessment to become a certified B Corp
The first step to becoming certified starts with the B Impact Assessment, a tool that will help us measure GER’s impact on our workers, community, environment, and customers on an 80-point scale. This means we’ll get to share features that have long been part of our company and company culture, like our commitment to diversity and inclusion.
Employee benefits
GER’s late founder Gary Kirkpatrick imbued the company with a spirit of generosity and compassion that permeates everything we do.
For example, we offer a comprehensive employee benefits package, including:
- Health insurance with 100% premium coverage. No one should ever have to question whether they can afford medical care.
- Competitive pay. Everyday living should not be a struggle.
- Competitive bonus plan. After a year of employment, everyone gets a share in GER’s success. When the company is doing well, all team members reap the benefits, whether they are managers or entry-level workers.
- Leadership training. Again, it doesn’t matter what position a team member holds. At GER, we want to empower everyone to be more.
Community support
In addition, Gary co-founded The Love House Kids Program, a nonprofit that works to break the cycle of child abuse by providing job training and one-on-one counseling. GER continues to support this important organization with monthly donations as well as physical support for fundraisers.
Environmental commitment
As an R2-certified electronics recycler, GER certainly undergoes rigorous annual third-party audits to ensure we comply with the highest environmental standards for our industry. R2 stands for Responsible Recycling and is a standard specifically created for the electronics recycling industry by Sustainable Electronics Recycling International. In other words, we believe we’re well equipped to fulfill the environmental requirements of becoming a certified B Corp.
Getting the seal of approval
Moreover, protecting people and the planet through electronics sustainability is at the heart of what we do. And it all starts right here at our facility in Phoenix, Ariz. Our passion statement also centers on the value of our people and creating an environment in which they can grow.
We have long shared with our customers and prospects our commitment to social responsibility. Becoming a certified B Corp would give us the seal of approval and show we back our promises with action. During the next 12 months, we will work hard to align every aspect of our company with the requirements of the B Corp Certification.
B Corps set the gold standard for good business and inspire a race to the top. How could we not officially join this force for good?
KEEP READING
Why the company culture of your e-recycler matters to your success
THE TELLTALE SIGNS OF DATA SANITIZATION DONE RIGHT
Data sanitization makes your data permanently unrecoverable, but don’t leave without verification.
Sometimes being careful is still not enough. While organizations rightfully pour resources into preventing data breaches while their electronic equipment is in use, what happens next? It is indeed equally important to establish protocols for end-of-life (EOL) equipment.
Read More